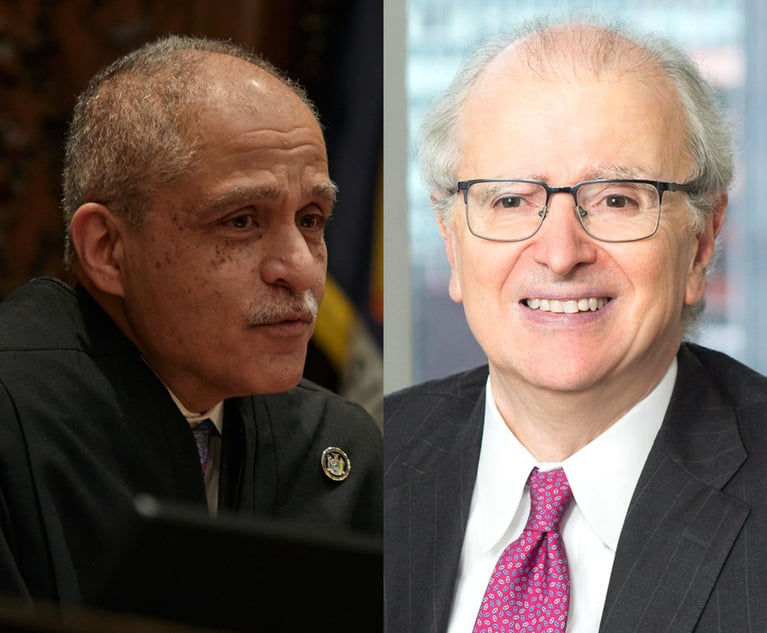
Divided FTC Finalizes Rule to Ban Noncompete Agreements
“First, in my mind, the plain text of the FTC Act clearly gives the agency the authority to promulgate rules addressing unfair methods of competition," FTC Chair Lina Khan said. Not everyone agrees.
5 minute read