Facebook has been making headlines lately over claims it shared personal data on more than 87 million people to the political data firm, Cambridge Analytica for use in the 2016 presidential election. In the midst of the Cambridge Analytica chaos, the Pennsylvania Superior Court provided long-overdue guidance on the authentication of posts from Facebook and other social media platforms. In the criminal case of Commonwealth v. Mangel, 2018 PA Super 57 (Mar. 15, 2018), a case of first impression in Pennsylvania, the Superior Court held that Facebook posts are not admissible without evidence, whether direct or circumstantial, substantiating the authorship of the messages, see Daniel E. Cummins, “Authentication in the Digital Age: In Recent Cases, Old and New Collide,” The Legal Intelligencer, April 5, 2018, and Zack Needles’ “Superior Court Adopts Standard for Authenticating Social Media Posts,” The Legal Intelligencer, March 21, 2018, for excellent discussions on the Mangel case.
In Mangel, defendants Tyler Mangel and Matthew Craft were charged with the simple and aggravated assault and harassment of Nathan Cornell at a graduation party. After he was assaulted, Cornell told the police he did not know the defendants, but could identify them as he was shown Facebook pictures by his family. The commonwealth filed a motion in limine to introduce screenshots of certain pages of a Facebook account for “Tyler Mangel,” consisting of undated online and mobile device “chat” messages. The commonwealth also sought to introduce a Facebook screenshot where a photograph of purportedly bloody hands had been posted by “Justin Jay Sprejum Hunt.”


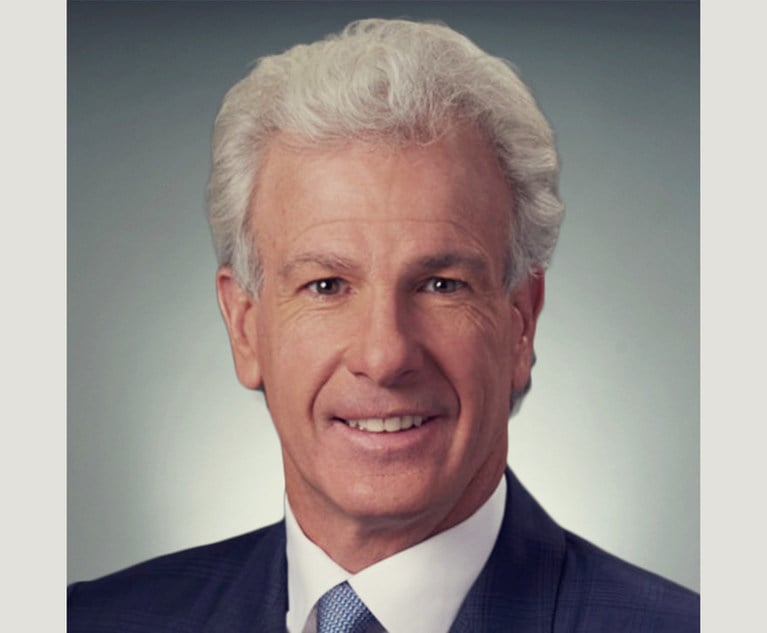
 Edward T. Kang of Kang Haggerty Fetbroyt.
Edward T. Kang of Kang Haggerty Fetbroyt.