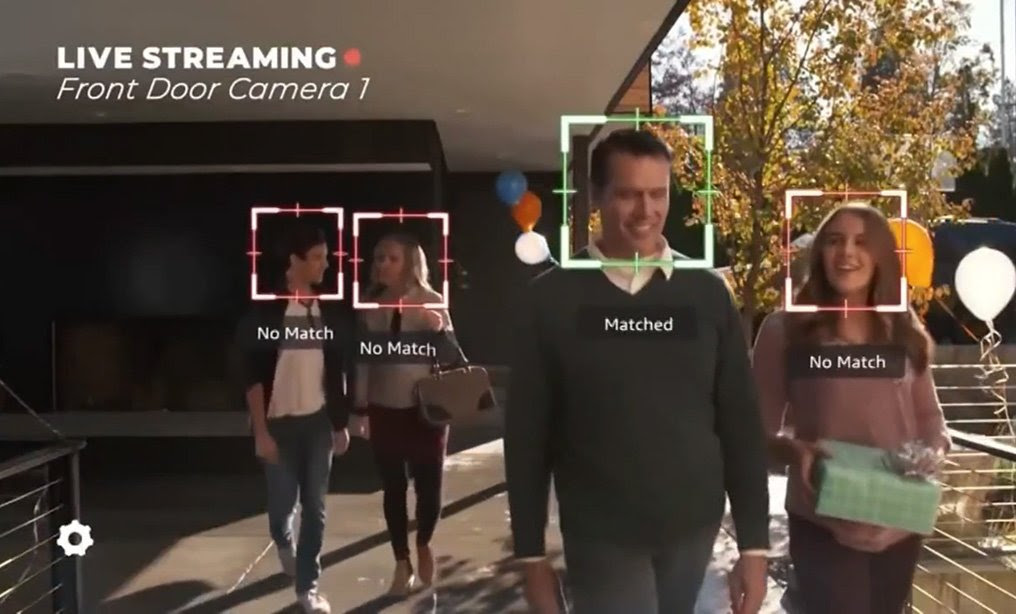
Welcome back for another week of What’s Next, where we report on the intersection of law and technology. This week, we take a look at a lawsuit accusing Apple of using facial recognition to accuse the wrong person of shoplifting. Plus, questions are surfacing again over when the government tells companies about software exploits it’s discovered. As always, thanks for reading.
➤➤ Would you like to receive What’s Next as a weekly email? Sign up here.